Table of Contents
What Is VRF?
VRF (Virtual Routing & Forwarding) is a technology for virtually separating the router. It is mainly used by PE routers that constitute MPLS-VPN. Note that the virtual separation of the router, regardless of MPLS, is referred to as VRF-Lite. However, the terms “VRF” and “VRF-Lite” are not used strictly in relation to MPLS or not. The term “VRF” is often used in situations where it is used regardless of MPLS.
VRF allows the creation of new, separate routing context VRF instances in the router. The routing context refers to the set of components necessary for routing, including the routing table, each routing process for building the routing table, and the associated interfaces.
Although it is very often described very simply as ” separate the routing table with VRF,” it is not only separate the routing table.
Creating a VRF and assigning interfaces to the VRF allows it to be treated as a virtual router with an independent routing table.
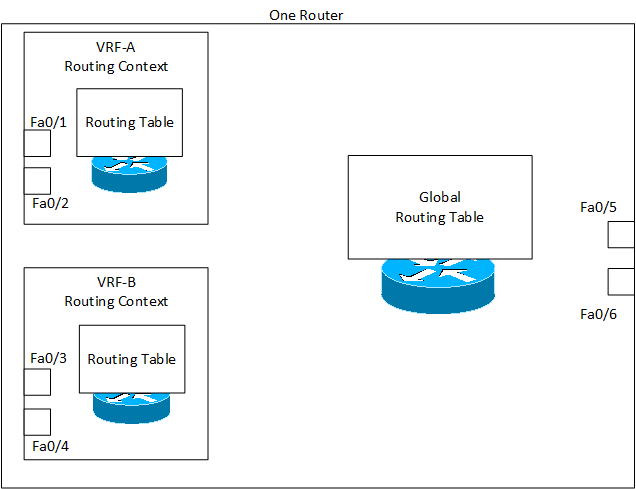
Virtual routers (routing contexts) divided by VRF cannot basically communicate with each other. Also, communication between the original global routing process and VRF is not possible. If communication between VRFs or between VRFs and the global routing process is needed, this can be done by configuring route leak. In other words, by default, VRFs are independent of each other, but if necessary, VRFs can communicate with each other.
Related articles
VRF route leak to provide communication between VRFs are described in the following article.
Uses of VRF
Packet filtering and route filtering are used to control the range of possible communication. However, conventional packet filtering and route filtering have limitations when trying to provide complex control. VRF allows for routing separation and flexible control over the range of possible communication. For example, it is easy to control the use of VRF in the following use cases.
- Layer 3VPN Service
- Separation of management network
Layer 3VPN Service
The following figure outlines the Layer 3 VPN service.
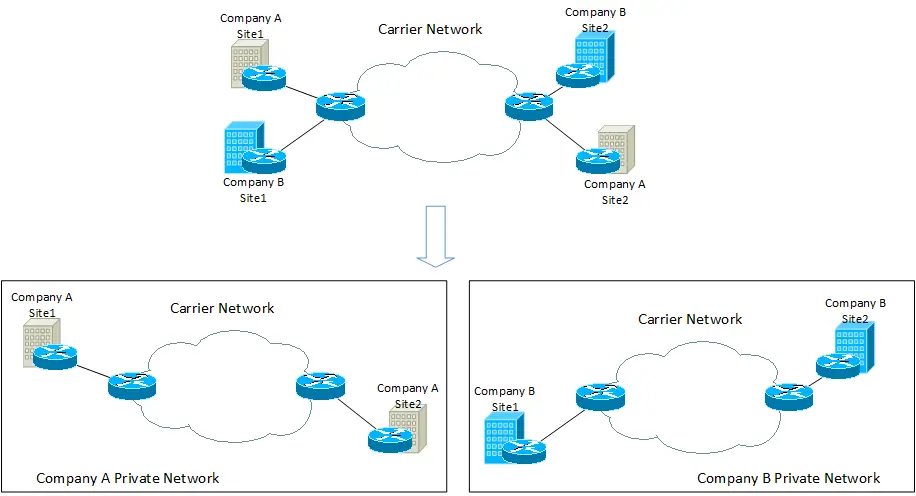
Two sites each of Company A and Company B are connected to the carrier network. The VRF prepares virtual routers for Company A and Company B. This makes it easy to build a Layer 3 VPN that allows communication only between Company A’s sites and between Company B’s sites.
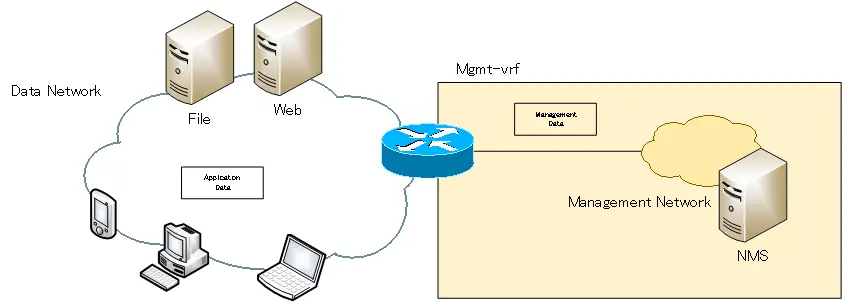
Separation of management network
Separating the network for transferring user data such as web browsers from the network for transferring management data such as Telnet/SSH and Syslog allows for more stable network management. VRF allows easy separation of data and management networks.
Related articles
The following article describes the VRF configuration and verification commands for Cisco.
An example of Layer 3 VPN configuration with VRF-Lite is described in the following article.
The following article describes an example configuration (FVRF) that separates overlay and underlay networks by VRF.
Advanced IP Routing
- Overview of Cisco Route-map
- Cisco Route-map Configuration
- GRE Tunnel Interface – Virtual Point-to-Point Connection
- GRE Tunnel Interface Configuration Example
- Overview of VRF/VRF-Lite – Virtually separating the router –
- Cisco VRF Configuration and Verification Commands
- Cisco Layer 3 VPN with VRF-Lite Configuration Example
- What Is FVRF(Front door VRF)?
- Point-to-point GRE Tunnel without FVRF
- Point-to-point GRE tunnel with FVRF (tunnel vrf command)
- IPSec VTI with FVRF
- IPSec VTI with FVRF Configuration Example
- DMVPN with FVRF
- DMVPN with FVRF Configuration Example Part1
- DMVPN with FVRF Configuration Example Part2