Table of Contents
CDP Overview
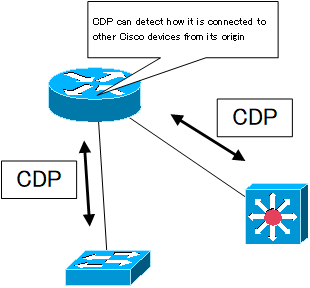
Cisco routers and Catalyst switches can use the Cisco Discovery Protocol (CDP) to discover other Cisco devices that are directly connected to them, starting with themselves. Directly connected devices are referred to as neighboring devices or adjacent devices.
CDP is a Cisco proprietary protocol that operates at the data link layer and is available on physical media that support SNAP encapsulation. physical media that support SNAP encapsulation include Ethernet, Frame Relay, ATM, and PPP/HDLC. It is also independent of higher-level protocols; note that because it is a Cisco proprietary protocol, it cannot be detected by network devices or hosts from other vendors.
Cisco routers/Catalyst switches have CDP enabled by default. it sends CDP information every 60 seconds. the reserved multicast address “01-00-0c-cc-cc-cc” is used to send and receive CDP information. receiving CDP information. and store its contents in the CDP cache. To see the CDP cache, use the show cdp neighbor command.
If it fails to receive periodic CDP information for a certain amount of time, it removes that information from the cache. This time is called the hold time, which defaults to 180 seconds.
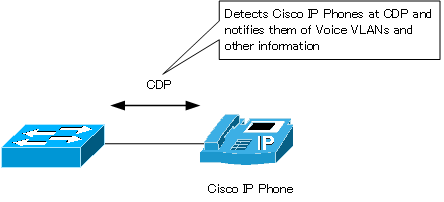
CDP is also used to discover the Cisco IP phones connected to the Catalyst switch. you can notify the Cisco IP phones connected to the Catalyst switch of the information needed for the IP phones, such as Voice VLANs.
Information exchanged via CDP
There are two versions of CDP: version 1 and version 2. Current Cisco devices have CDP version 2 enabled by default.
In CDP version 1, the following information is sent and received
- Neighboring device ID
- Local interface
- Neighboring device capability
- Neighboring device platform
- Remote interface
- Network layer address of neighboring devices
- IOS version of neighboring devices
In addition to this, CDP version 2 adds the following information
- VTP domain name
- Native VLAN
- Duplex mode of interface
Disabling CDP
The information exchanged by CDP includes IOS version and IP address information. Therefore, inadvertently sending information via CDP could provide a foothold for a malicious cracker to gain unauthorized access. Also, if the directly connected device is not made by Cisco, there is no point in sending CDP information. So, you need to control the enabling/disabling of CDP.
To disable CDP, enter the following command in global configuration mode.
(config)#no cdp run
To enable CDP again, enter the cdp run command.
And you can disable CDP on a per-interface basis as well. enter the following command in the interface configuration mode where you want to disable CDP.
(config-if)#no cdp enable
This configuration stops the CDP information from being sent from the corresponding interface. To enable CDP again, enter the cdp enable command.
Verification of CDP
To verify the Cisco devices directly connected by CDP, you can use the following main commands.
- #show cdp neighbor [detail]
- #show cdp entry <device-id>
The following is an example of show cdp neighbor output.
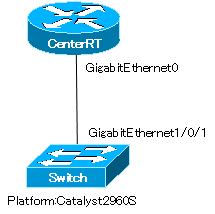
CenterRT#show cdp neighbors
Capability Codes: R - Router, T - Trans Bridge, B - Source Route Bridge
S - Switch, H - Host, I - IGMP, r - Repeater, P - Phone,
D - Remote, C - CVTA, M - Two-port Mac Relay
Device ID Local Intrfce Holdtme Capability Platform Port ID
Switch Gig 0 179 S I WS-C2960S Gig 1/0/1
The hostname of the device running the show cdp neighbor command is CenterRT. the CenterRT is directly connected to the Switch. The interfaces that are connected are as follows.
CenterRT GigabitEthernet0 (Local Intrfce)
Switch GigabitEthernet1/0/1(Port ID)
You can also see from the Platform that the Switch is a Catalyst 2960S.
To find out more information about CDP, use the show cdp neighbor detail or show cdp entry <device-id> command.
CenterRT#show cdp neighbors detail ------------------------- Device ID: Switch Entry address(es): 10.0.0.100 Platform: cisco WS-C2960S-24TS-L, Capabilities: Switch IGMP Interface: GigabitEthernet0, Port ID (outgoing port): GigabitEthernet1/0/1 Holdtime : 177 sec Version : Cisco IOS Software, C2960S Software (C2960S-UNIVERSALK9-M), Version 15.0(2)SE2, RELEASE SOFTWARE (fc1) Technical Support: http://www.cisco.com/techsupport Copyright (c) 1986-2013 by Cisco Systems, Inc. Compiled Tue 05-Feb-13 12:48 by prod_rel_team advertisement version: 2 Protocol Hello: OUI=0x00000C, Protocol ID=0x0112; payload len=27, value=00000000FFFFFFFF010231FF00000000000070105C247880FF0000 VTP Management Domain: 'cisco' Native VLAN: 1 Duplex: full
The show cdp neighbor detail command also shows various information such as IP address, IOS version, VTP domain, native VLAN, duplex, and more.
Cisco Basic
- Preparing for Cisco devices configuration
- Configuration files for Cisco devices
- The configuration steps for Cisco devices
- Basic knowledge of the Cisco CLI: Command types and modes
- Cisco device’s interface
- CLI help and completion
- The main error messages in CLI
- Cisco Deleting a configuration command
- default interface command -Initialize the interface settings-
- Entering commands in batches
- do command – Execute EXEC command from configuration mode –
- interface range command -Batch configuration of multiple interfaces-
- Filtering the display of the show command – displaying only the information you want to see –
- Cisco IOS Name Resolution Configuration
- terminal length command : configuration of the number of lines displayed in the command output
- debug command to verify real-time operation
- Automatically enter privileged EXEC mode upon CLI login
- Configure System Clock
- Saving and managing configuration files
- Version Management of Configuration Files ~archive command
- IOS File System Operations
- Managing Cisco Catalyst Switches :What it means to set an IP address on a switch.
- Remote management by VTY access (Telnet/SSH)
- terminal monitor command to display the log of Telnet/SSH login destination
- Multi-step Telnet Session Suspensions
- Set the minimum number of characters in the password [Cisco]
- Restrict login attempts : login block-for command
- Cisco Initial Configuration Example
- CDP – What are the connected devices? –
- Password recovery for Cisco routers
- Password Recovery for Catalyst Switches